The privacy and security of your protected health information is very important to LANES. We are committed to safeguarding your information. Therefore, we prioritize your protection with a continuously advancing privacy and security posture through a series of key initiatives and projects..
SECURITY & PRIVACY
Security and privacy are at our core at LANES as a HITRUST CSF Certified Organization. LANES patient data privacy and security safeguards meet and exceed federal, state, and local requirements. These include the HIPAA Privacy Rule, HIPAA Security Rule, and HITECH Act. We work diligently to examine and uphold the complexities of patient consent through continual consultation with legal experts in HIPAA and our community privacy and security experts serving on the LANES Privacy & Security Advisory Board.
LEADERSHIP
LANES maintains a managed IT and security infrastructure which includes an internal IT team, an internal security team, and a managed service provider.
LANES has designated a Chief Information Security Officer (CISO) and a Privacy Officer to oversee a comprehensive information security and privacy program, including a robust risk management program.
The Security and Privacy Advisory Committee was established to provide strategic thought leadership and develop our Privacy Policy.
PRIVACY
Collection: We collect from you Personally Identifiable Information and Protected Health Information.
Permitted Uses: Your patient data is only used for treatment, payment, operations, continuity of care, and case management to improve the quality of your healthcare.
Consent: You are in control of sharing your information, and we focus on the consent you provide to your provider. We will not disclose your medical information without your written authorization unless it’s specifically permitted or required by law.
Rights: Under the CCPA, CPRA, the Confidentiality of Medical Information Act (CMIA), and applicable laws and regulations:
- You have the right to request access to your personal health information that is stored by LANES. Upon request, we will provide you with the specific pieces of personal information we have collected about you, the categories of sources from which it was collected, the business purpose for collecting or selling the information, and the categories of third parties with whom we share it.
- You also have the right to request the deletion of your personal information that we have collected. Upon verifying your request, we will delete your personal information from our records unless it’s necessary for our business purposes or required to be retained by law.
- We do not sell your personal information. If in the future we choose to sell information, you will be provided with the right to opt-out of such sales.
- We respect your privacy rights and ensure that we do not discriminate against you for exercising any of your CCPA rights.
- You have the right to correct inaccuracies in your personal information. Furthermore, we limit the use of sensitive personal information as defined by the CPRA and use it only for necessary business purposes.
- You have the right to know who is accessing your information. Upon your request, we will provide an accounting of disclosures of your medical information made by us, detailing where and to whom your information has been shared.
- You have the right to request restrictions on certain uses and disclosures of your medical information, as outlined in the CMIA. We will do our best to honor your request.
- You have the right to access and obtain a copy of your medical information. To request access or a copy, please contact your health care provider.
Internal Access: Only those who require access to the systems are given access (role-based access); all access is monitored and reviewed regularly.
Breach Notification: CMIA requires entities to notify patients when certain types of unauthorized access, use, or disclosure of medical information occur. In the unlikely event of an unauthorized access, use, or disclosure of your medical information, we will promptly notify you as required by the Act.
Privileged Account Management – Privileged accounts are secured and managed with MFA.
SECURITY
Data Security: Sensitive data resides in a HIPAA-compliant, HITRUST-certified AWS cloud platform. Multiple security controls are in place to protect against unauthorized access to sensitive and confidential data:
- Role-based access control leveraging the principle of least privilege.
- Network segmentation of servers containing sensitive data.
- MFA required for all users.
- Logging and monitoring.
Data Backup & Recovery: All servers and online databases are included in our backup strategy. Systems and data are backed up daily using offside backup (AWS S3). Local backups are protected against deletion or corruption using the following strategies:
- MFA is required for access to the backup management interface.
- MFA is required for access to backup files.
- Backup servers are not joined to a Windows domain.
- Backups servers and user accounts leverage unique credentials.
- Backup servers are segmented from the rest of the network.
- A backup solution has been developed with immutable backups.
- Copies of backup are kept offline or air gapped.
- A Business Continuity Plan and a Disaster Recovery Plan are in place.
- Integrity of backups and the disaster recovery plan are tested quarterly.
Encryption: We secure our networks and environments with strong AES 256 encryption for data in transit and at rest. Sensitive data is encrypted across systems and devices using:
- Full disk encryption;
- Mobile device encryption;
- Data-in-transit; and
- AWS S3 encryption.
Authentication: We require strong, complex passwords for access to systems. Multi-Factor Authentication (MFA) is enforced for all employees and Microsoft Defender is our email security solution with the following features enabled:
- Spam and phishing protection;
- User impersonation protection;
- Attachment sandboxing;
- URL sandboxing;
- Blocking executable file attachment extensions; and
- Blocking macro-enabled Microsoft Office documents.
Phishing Security: Training on the threats of phishing is completed upon hire and annually therein. Phishing simulations are conducted quarterly.
Endpoint & Network Security: A Virtual Private Network (VPN) is used to allow authorized users to connect into the environment while outside the office and MFA is enforced for remote access to the network. LANES uses Microsoft Defender antivirus, Rapid7 endpoint detection, and Intune endpoint security technologies. pfSense+ is used for a traditional firewall; and pfSense+ and Rapid7 are used for IDS/IPS.
Protection: We administer security controls administered on network and environments that are tested and validated, such as Data Loss Prevention (DLP) and MFA protocols.
Integrity: We guard your data by routinely monitoring, logging and auditing protocols in place to keep your data secure and up to date.
Disaster Recovery: We have a full Disaster Recovery Plan and a set of Business Continuity of Operations procedures, with a secondary, geographically divided site available if necessary.
Vulnerability Management Program. We have a rigorous vulnerability assessment protocol, including at least annual penetration tests and quarterly vulnerability scans.
Patch Management Program: We maintain a patch management policy and procedure to mitigate identified vulnerabilities.
REGULATORY COMPLIANCE AND INDUSTRY BEST PRACTICES
HIPAA: We are compliant with both the Security Rule and the Privacy Rule for the protection and safeguarding of Protected Health Information (PHI).
HITRUST: We are HITRUST certified, meeting the HITRUST® CSF v9.2 certification criteria.
California and Federal Guidelines: We also comply with all privacy regulations for the state and federal government regarding data and information collection. This includes, but is not limited to, the CCPA, the CPRA, and the CMIA.
Risk Management: We use a risk-informed decision-making process to manage privacy and security risk to you, to your data and for our systems.
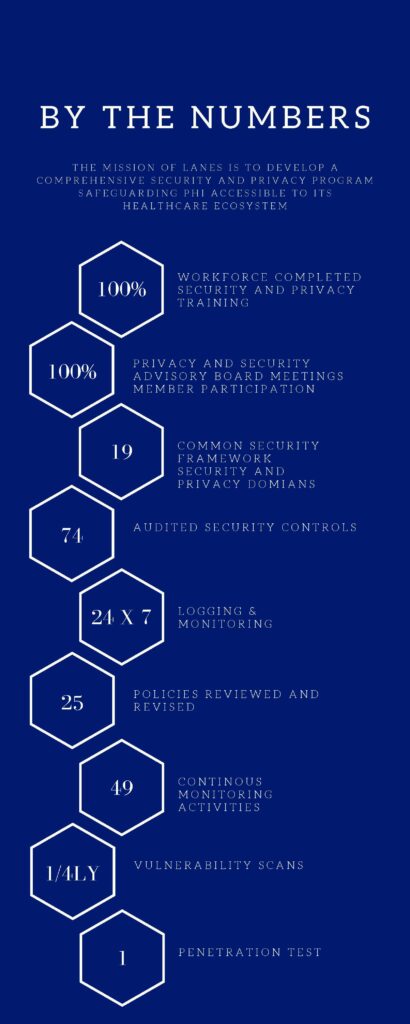
Key Performance Indicators (KPIs): LANES measures and manages progress against a series of Key Performance Indicators that track progress toward safeguarding systems and data.
Continuous Monitoring Program: We have implemented a Continuous Monitoring Plan that tracks compliance with controls as delineated in the entire set of security and privacy policies and are mapped to the HITRUST domains and to the identified KPIs.
VENDOR MANAGEMENT
We will not disclose your medical information without your written authorization unless it’s specifically permitted or required by law.
When sharing medical information with our trusted providers or contractors, they are bound by the same stringent privacy protections. They are not allowed to use your medical information beyond the scope of privacy protections outlined in this Policy
The LANES CISO maintains a security-based risk management approach to working with vendors and third parties. The LANES Privacy Officer examines relationships with vendors and third parties through the lens of data protection and privacy.
LANES has established a direct line of communication with the security team at the key technology vendor (NextGen – Mirth) to stay on top of identified security questions and monitor the partnership. We consistently receive and implement guidance regarding the ecosystem’s security and privacy postures from LANES executives, key stakeholders and participant organizations.